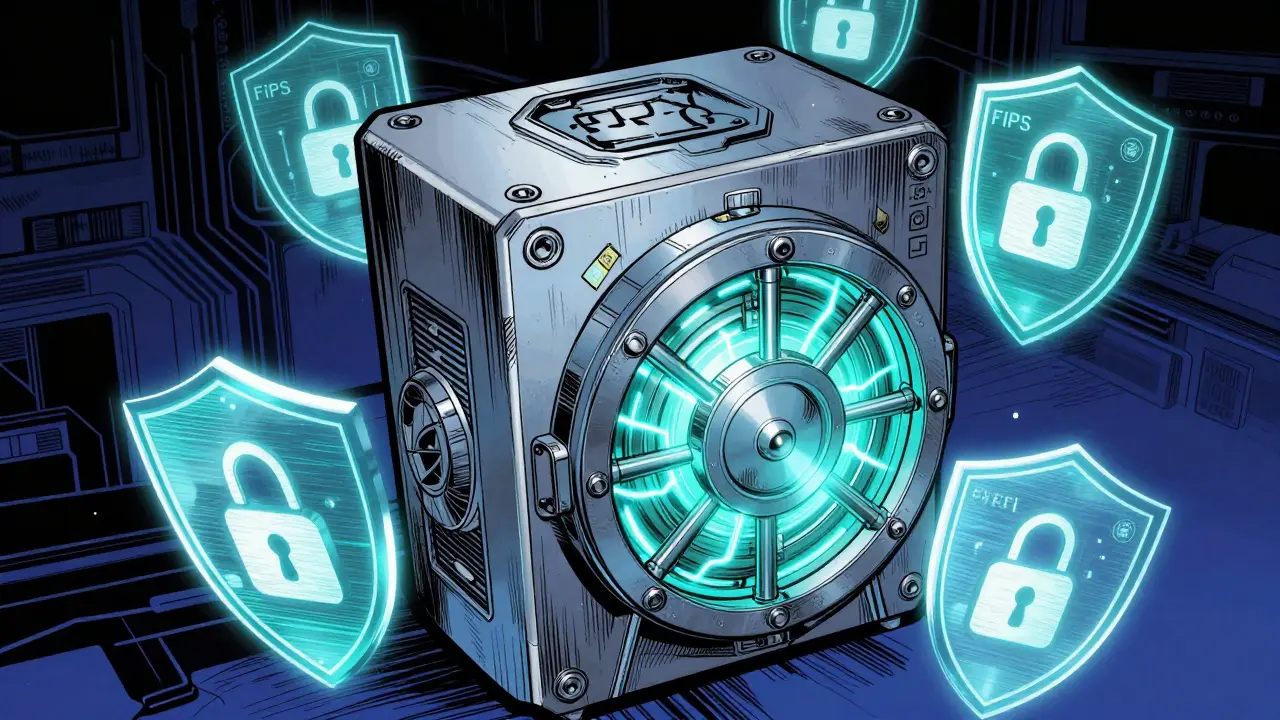
If you are managing digital assets or processing high-value transactions, you know that software encryption isn't enough. To truly lock down private keys, you need a Hardware Security Module is a physical computing device that safeguards and manages digital keys, performs encryption and decryption functions, and provides strong authentication. Commonly known as an HSM, it acts as the Root of Trust for the entire security architecture. But here is the catch: an HSM is only as trustworthy as the certifications backing it. Without official compliance, you're essentially taking a vendor's word that their "unbreakable" box actually works.
Navigating the alphabet soup of FIPS, PCI, and EAL can be a nightmare. Whether you're building a blockchain bridge, a payment gateway, or a corporate treasury, you need to know which certification actually matters for your specific use case. If you pick the wrong one, you might find yourself failing an audit or, worse, discovering a physical vulnerability that allows an attacker to extract your keys.
The Gold Standards: FIPS and PCI PTS
Most organizations start their search with two heavy hitters: NIST and the PCI Security Standards Council. These aren't just "suggestions"; for many industries, they are legal or contractual mandates.
FIPS 140-2 (and the newer FIPS 140-3) is the benchmark set by the National Institute of Standards and Technology (NIST). It defines how a cryptographic module must be built to resist attacks. FIPS uses a tiered system from Level 1 to Level 4. While Level 1 is basic, an enterprise-grade HSM often aims for Level 3 or 4. At Level 4, the device is designed to survive extreme environmental attacks, such as voltage fluctuations or temperature spikes, which hackers use to glitch a chip into revealing its secrets.
Then there is the PCI PTS HSM standard. If you are touching credit card numbers or PINs, this is your bible. The Payment Card Industry PIN Transaction Security standard focuses heavily on the entire lifecycle of the device-from the factory where it's built to the moment it's shipped to your data center. It ensures that no one can sneak a "backdoor" into the hardware during transit.
| Certification | Primary Focus | Key Attribute | Best For |
|---|---|---|---|
| FIPS 140-2/3 | Cryptographic Robustness | Security Levels (1-4) | Govt, Enterprise, General Encryption |
| PCI PTS HSM | Payment Security | Lifecycle Management | Banking, ATMs, Payment Gateways |
| Common Criteria | Functional Behavior | EAL Levels (e.g., EAL4+) | EU Trust Services, eIDAS, Signatures |
Physical vs. Logical Security: What's Actually Being Tested?
When an auditor looks at an HSM, they aren't just checking the code. They are looking for physical evidence of tamper-resistance. Under the PCI PTS HSM v3.0 requirements, a device must have mechanisms that cause immediate inoperability if someone tries to drill into the casing or open the chassis. This usually involves a "mesh" of fine wires; if one wire is broken or shorted, the HSM triggers a zeroization process, instantly erasing all sensitive keys.
But physical armor is only half the battle. Logical security governs the firmware and the management protocols. This is where things get tricky for users. An HSM's certification is tied to a specific version of its firmware. If you install a custom plugin or a non-approved firmware update, your HSM Compliance status vanishes instantly. You might have the most expensive hardware in the world, but if the software version doesn't match the approved listing on the PCI certificate, you are technically non-compliant.
The Trust Services Path: Common Criteria and eIDAS
If your project involves electronic signatures or trust services in Europe, FIPS might not be enough. You'll likely need Common Criteria validation. Unlike FIPS, which is a set of requirements, Common Criteria is a framework. You use a "Protection Profile" (like EN 419221-5:2018) to define what the device is supposed to do, and then it's tested against that profile.
The goal here is often an EAL4+ rating. This is critical for anyone operating under the eIDAS regulation, which governs electronic identification and trust services in the EU. If you are running a Qualified Signature Creation Device (QSCD), Common Criteria is the only way to prove your HSM behaves as promised within a larger security architecture.
The Customization Trap
Here is a real-world scenario: You buy a certified HSM, but your blockchain application requires a specific, non-standard cryptographic curve. Your vendor offers to write a custom software module for you. Sounds great, right? Wrong.
The moment you run custom code on that device, the original certification is voided. To get that custom version certified, you'd have to put the device back through the entire evaluation process, which can cost tens of thousands of dollars and take months. This creates a massive tension between the need for flexibility and the need for assurance. Most companies end up sticking to the "standard" certified functions, even if they are slightly less efficient, just to avoid the certification nightmare.
Cloud HSMs: Shifting the Trust Model
Not everyone can afford a physical room with biometric locks and cages. This has led to the rise of Cloud HSMs. Services like Azure Payment HSM or IBM Cloud now offer certified modules as a service. They claim compliance with a huge range of standards, including PCI DSS, PCI PIN, and even ISO 20000-1.
When using a cloud provider, you aren't managing the physical tamper-mesh, but you are still responsible for the logical configuration. The beauty of the cloud model is that the provider handles the firmware updates and the tedious process of maintaining certification with the councils. However, you are trading physical control for a service-level agreement (SLA). You have to trust that the provider's orchestration layer isn't introducing a vulnerability that bypasses the HSM's hardware protections.
What happens if I update my HSM firmware?
If you install firmware that hasn't been approved by the certification body (like the PCI Council), your device immediately loses its compliance status. You must check the official approved listing for the specific version identifier before updating to ensure you remain compliant.
Is FIPS 140-2 the same as FIPS 140-3?
No. FIPS 140-3 is the successor to 140-2. It incorporates more modern cryptographic algorithms and addresses newer types of attacks. While many systems still rely on 140-2, new hardware is moving toward 140-3 to stay current with NIST standards.
Can one HSM have multiple certifications?
Yes, and it's actually the industry standard. Most high-end HSMs carry both PCI PTS and FIPS certifications. This allows them to be used in both government environments and payment processing pipelines without needing separate hardware.
What is "Zeroization" in the context of HSMs?
Zeroization is the process of instantly erasing all plaintext cryptographic keys from the device's memory. This is triggered automatically if the HSM detects a physical breach, such as the casing being opened or a probe being inserted into the circuitry.
Do I need Common Criteria for a US-based project?
Not necessarily, unless you are dealing with specific international trust services or European regulations like eIDAS. For most US-based federal or corporate projects, FIPS 140-2/3 is the primary requirement.
Next Steps for Deployment
If you're just starting, don't buy hardware based on a marketing brochure. Ask the vendor for the actual certification numbers and the approved firmware list. If you are in the payments space, prioritize PCI PTS HSM v3.0. If you are building a general-purpose secure vault, look for FIPS 140-3 Level 3.
For those moving to the cloud, verify that the provider gives you a "dedicated" HSM instance rather than a shared one. Shared environments can be compliant, but dedicated modules provide a much cleaner audit trail for your Qualified Security Assessor (QSA).


Yuhan Mo
April 15 2026The transition from FIPS 140-2 to 140-3 is a critical pivot for the industry, especially with the deprecation of legacy algorithms and the move toward more robust side-channel attack mitigations. It's a bit of a headache for legacy system integration, but the security posture improvement is non-negligible.
Abhinav Chaubey
April 17 2026It is quite amusing that people still believe the US-centric FIPS is the only benchmark that matters when the global market is shifting. India's fintech infrastructure is far more agile and we deal with these standards every day without needing a simplified guide for the masses. Most of these 'complexities' are just administrative hurdles for those who aren't actually in the trenches of high-scale implementation.
Michelle Stanish
April 18 2026FIPS is overkill for most.
Kim Smith
April 19 2026it's just so wild to think about the sheer human effort that goes into these certifications, like, imagine some poor soul spending their whole career just checking if a wire mesh actually triggers a zeroization event because the idea of an absolute root of trust is such a beautiful but fragile concept in our chaotic digital universe, and honestly, the way we trust these big boxes just because a gov agency says so is almost a spiritual exercise in faith, dont you think, cause at the end of the day, we're just layering boxes inside boxes hoping the bad guys dont find the one loose screw in the whole machine... it's kind of a metaphor for life really.
Alex Long
April 21 2026boring stuff. just use a cloud hsm and stop pretending you're doing something special.
siddharth narula
April 23 2026One must ponder the ethical implications of placing absolute trust in a piece of silicon. Is the pursuit of a "certified" box merely a shield for the corporate soul to avoid true accountability? 🧐 The pursuit of perfection in security is a noble but ultimately futile endeavor in a world governed by entropy. 🏛️
Robert Preston
April 24 2026The zeroization process is the only thing that actually saves your skin during a physical breach. If you aren't auditing the physical tamper-evidence daily, you're basically leaving the door open. You need to be assertive with your vendors about the exact trigger mechanisms of that mesh.
Adedamola Oyebo
April 25 2026Cloud HSMs are a game changer!! However, the orchestration layer is still a massive risk factor!! Always check the shared responsibility model!!
Anna Grealis
April 26 2026the vendors lie about the mesh. its all a scam to make you pay more for 'level 4' hardware that probable has a backdoor built in by the nsa anyway. dont trust the certs, trust nobody. everything is compromised already.
Saurav Bhattarai
April 26 2026Imagine thinking that a few wires in a box can stop a determined state actor. How quaint! The Western obsession with these checkboxes is purely for the sake of audit theatre. In the real world, we know that the only real security is knowing exactly who is writing the code, and frankly, most of these FIPS-certified modules are just slow and overpriced bricks.
Jeff Barlett
April 28 2026Actually, the 'customization trap' is a total myth. Plenty of people run custom code on HSMs. They just don't tell the auditors. Who cares about a piece of paper from the PCI council if the encryption actually works?
Keri Pommerenk
April 30 2026I agree with the point on firmware updates. It is so easy to forget that a simple patch can wipe your compliance status
Kaitlyn Wu
April 30 2026For anyone starting out, just remember that compliance does not equal security. You can be 100% FIPS compliant and still have a terrible key management policy that allows a junior dev to accidentally leak the master key via a config file. Get your house in order first.
Tracy Sperandio
May 1 2026This is a dazzling breakdown of a normally dry topic! Let's get some energy into this-don't let the alphabet soup drown you! Just dive into the FIPS 140-3 specs and conquer your data center!
Karen Mogollon Gutierrez
May 3 2026It is simply appalling that the industry allows such a fragmented landscape of certifications to exist. The sheer inefficiency of having to navigate both Common Criteria and FIPS for a single global product is an absolute tragedy of modern engineering!
nikki krinkin
May 5 2026I appreciate the heads up on the eIDAS requirements. It's a lot to keep track of but it makes sense for the EU market.
Evan Iacoboni
May 6 2026Wait, if a custom plugin voids the certification, does that mean the hardware is actually less secure, or just that the paperwork is gone?
Nishant Goyal
May 7 2026Good summary. Keep it simple.
nathan jones
May 8 2026FIPS is the way to go for most US projects.